Stránka 25 z 26
Re: Intel CPU design flaw |Meltdown, Spectre a ine|
Napsal: čtv 16. led 2020, 09:26
od Krteq
Re: Intel CPU design flaw |Meltdown, Spectre a ine|
Napsal: sob 18. led 2020, 12:30
od hnizdo
https://www.phoronix.com/scan.php?page= ... or-No-Loss
**** NOTE: ****
This series is in active development and is not intended to be merged to mainline in its current form. The intent of the RFC is simply to outline the strategy for the mitigation, as a focus for active discussion, and to openly share progress. There has been only minimal attention paid to performance thus far, as the focus is on robustness. It is not anticipated that there will be any measurable performance impact in the final version.
**** END NOTE ****
Takze klasika. Prvni mereni desitky procent v nekterych benchmarcich, v praxi vsechny patche dohromady 5%.
Re: Intel CPU design flaw |Meltdown, Spectre a ine|
Napsal: úte 28. led 2020, 08:38
od Krteq
Re: Intel CPU design flaw |Meltdown, Spectre a ine|
Napsal: úte 28. led 2020, 08:50
od hnizdo
Additionally, the following specifically states that physical admin access(authenticated local access) is required;
https://blogs.intel.com/technology/2020 ... -sa-00329/
An attack to exploit this vulnerability can not be rendered remotely, IE through a network share or web browser.
Re: Intel CPU design flaw |Meltdown, Spectre a ine|
Napsal: pon 9. bře 2020, 00:54
od killerek
Re: Intel CPU design flaw |Meltdown, Spectre a ine|
Napsal: pon 9. bře 2020, 08:59
od hnizdo
https://arstechnica.com/information-tec ... unfixable/
Exploiting the vulnerability—particularly reading the chipset key—would be a major technical feat that would require specialized gear and years of experience with firmware.
a potential exploit for this issue appears to be fairly complicated, involving multi-stage chain compromising ISH or other firmware [and] then mounting a DMA [direct memory access] attack against CSME
Takze potrebujeme fyzicky pristup k PC, experta na firmware, specialni vybaveni a zda se jeste trochu stesti. Praktickou vyuzitelnost v dobe, kdy se hacker dostane do jakychkoliv desitek behem 17ti minut (ted mel probehnout nejaky contest ci co), ponechavam k volne fantazii.
Re: Intel CPU design flaw |Meltdown, Spectre a ine|
Napsal: úte 10. bře 2020, 18:43
od Krteq
Včera konkurence, dnes opět Intel a tentokrát v pořádným gardu

Load Value Injection (LVI) is being disclosed today as a new class of transient-execution attacks and the researchers claim can defeat all existing mitigations around Meltdown, Foreshadow, Zombieload, RIDL and Fallout. The researchers say LVI can affect virtually any access to memory and compiler-based mitigations can be expensive.
LVI mitigations amount to inserting lfence barriers before every vulnerable load instruction. The researchers also believe that certain instructions need to be blacklisted. The researchers found the prototype compiler-based mitigations have an Intel SGX performance hit of 2x to 19x but the actual real-world impact may differ
Re: Intel CPU design flaw |Meltdown, Spectre a ine|
Napsal: stř 11. bře 2020, 06:56
od hnizdo
No a já doplním další podstatnou věc, která ti jako obvykle vypadla
Intel has published a full analysis of the LVI flaw, stating that "Due to the numerous, complex requirements that must be satisfied to implement the LVI method successfully, LVI is not a practical exploit in real-world environments where the OS and VMM are trusted[..] Accordingly, system administrators and application developers should carefully consider the particular threat model applicable to their systems when deciding whether and where to mitigate LVI."
Čili nejen že se to týká jen datacenter a sgx zároveň, ale ještě jen na teoretické úrovni.
EDIT:
The difficulty in carrying out LVI attacks isn’t the only limitation. The data the attacks can acquire is also restricted to that stored at the time the malicious code is executed. That makes exploits either a game of luck or further adds to the rigorous requirements for exploitation. For those reasons, many researchers say they’re unsure exploits will ever be used in active malicious attacks.
https://arstechnica.com/information-tec ... e-enclave/
Re: Intel CPU design flaw |Meltdown, Spectre a ine|
Napsal: stř 11. bře 2020, 12:50
od Krteq
A další nálož publikovaná včera společně s LVI
Re: Intel CPU design flaw |Meltdown, Spectre a ine|
Napsal: čtv 12. bře 2020, 08:18
od fobos
V CPU Intelu nalezena další bezpečnostní chyba: Load Value Injection
Nalézání bezpečnostních chyb v procesorech je už téměř na denním pořádku a nyní tu máme další objevenou chybu. Jde opět o procesory Intelu a chyba Load Value Injection postihuje zejména Software Guard Extensions (SGX).
/sry som slepy, ale tak aspon to mate po cesky

Re: Intel CPU design flaw |Meltdown, Spectre a ine|
Napsal: pát 13. bře 2020, 08:56
od Krteq
Re: Intel CPU design flaw |Meltdown, Spectre a ine|
Napsal: pát 13. bře 2020, 14:50
od hnizdo
krtku, mas to vazne zapotrebi?

LVI cannot be transparently mitigated in existing processors and necessitates expensive software patches, which may slow down Intel
SGX enclave computations 2 up to 19 times.
https://arstechnica.com/information-tec ... e-enclave/
Na jinem miste vyzkumnici upozornuji, ze po uprave kompileru a po zahrnuti doporuceni intelu se muze postih zmirnit.
Re: Intel CPU design flaw |Meltdown, Spectre a ine|
Napsal: ned 5. dub 2020, 19:23
od Krteq
Re: Intel CPU design flaw |Meltdown, Spectre a ine|
Napsal: pon 6. dub 2020, 20:34
od Krteq
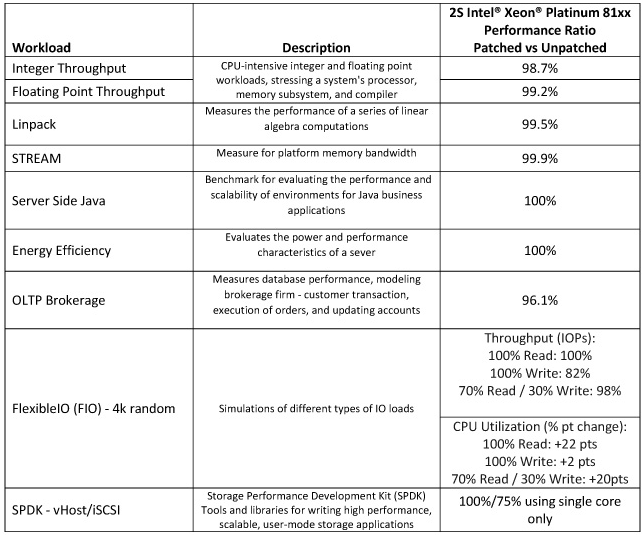
Benchmarks measuring integer and floating point throughput, as well as LINpack runs and STREAM memory performance tests and server-side Java, showed negligible difference between patched and unpatched systems, Intel noted. The difference was between zero and two percent.
The story was different with I/O loads, however.
With the FlexibleIO benchmarks, stressing the CPU fully during writes saw an 18 percent decrease in performance, because there was no headroom for processor utilisation, Intel said.
With low processor stress, there was no performance impact with patched systems, but CPU utilisation increased compared to unpatched servers.
Testing with storage performance development kit (SPDK) tools revealed a 25 percent performance hit when using the internet protocol-based iSCSI benchmark, using a single processor core.
"Generally speaking, the workloads that incorporate a larger number of user/kernel privilege changes and spend a significant amount of time in privileged mode will be more adversely impacted," Intel's data centre group head Navin Shenoy said.
IT-News: Data centre storage performance hurt by Meltdown-Spectre patches
-------------------------
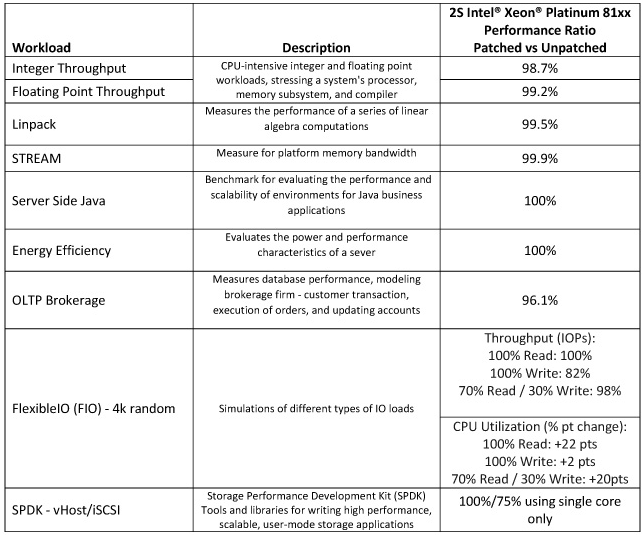 SecurityWeek - Intel Tests Performance Impact of CPU Patches on Data Centers
SecurityWeek - Intel Tests Performance Impact of CPU Patches on Data Centers
-------------------------
Podobné dopady jsme měli na našem VDI prostředí (cca. 5K VMs) - od času 29:11
Login VSI - Intel MDS Patches and VDI Density Performance [Webinar - July 2019] / YouTube
//Baneshee - promaz OT. Držte se faktů, není zde volná diskuze na téma "co si myslíte o chybách v CPU a tak vůbec"
Re: Intel CPU design flaw |Meltdown, Spectre a ine|
Napsal: sob 30. kvě 2020, 22:12
od Krteq
Re: Intel CPU design flaw |Meltdown, Spectre a ine|
Napsal: úte 9. čer 2020, 16:46
od Krteq
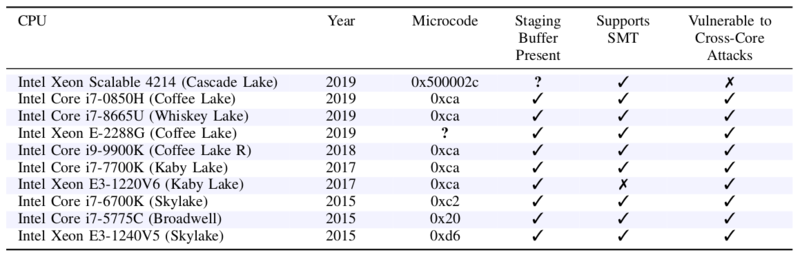
Další do řady
CrossTalk (INTEL-SA-00320 / CVE-2020-0543)
Re: Intel CPU design flaw |Meltdown, Spectre a ine|
Napsal: stř 10. čer 2020, 17:39
od Krteq
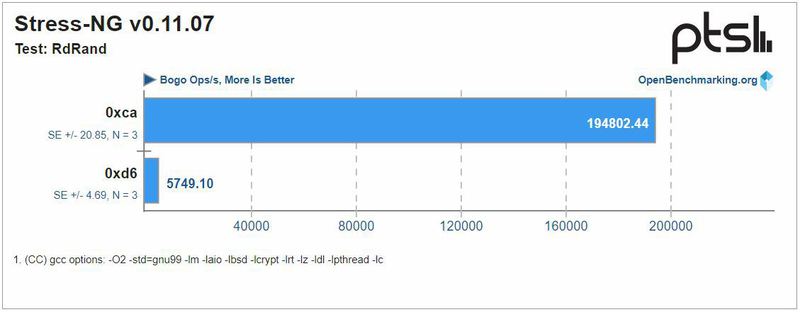
Výkonostní propady po aplikaci firmwaru s fixem
Phoronix.com - Benchmarking The Updated Intel CPU Microcode For SRBDS / CrossTalk Mitigation
SQL dostává další ránu a cokoliv co používá instrukce pro generování náhodných čísel RDRAND, RDSEED a EGETKEY je kvůli izolaci naprosto nepoužitelné

Re: Intel CPU design flaw |Meltdown, Spectre a ine|
Napsal: stř 10. čer 2020, 17:54
od hnizdo
Naposto nepouzitelne, prelozeno do reality:
The "good" news is that RdRand isn't used prolificily by real-world workloads. So when stressing a wide range of server-ish workloads, the overall impact from the SRBDS mitigation was not impacted to within a few percent the original performance as a worst case. It was just in a few cases the SRBDS mitigated microcode slightly lowered performance while for most tests the performance was fortunately stable.
Re: Intel CPU design flaw |Meltdown, Spectre a ine|
Napsal: stř 10. čer 2020, 21:47
od Krteq
Tak určitě

Málem bych zapomněl na další nově uveřejněnou chybu, ale spadající pod CacheOut
SGAxe
Re: Intel CPU design flaw |Meltdown, Spectre a ine|
Napsal: stř 10. čer 2020, 22:12
od hnizdo
Ano, zcela urcite.
When it came to evaluating different desktop workloads on the Core i5 8400, the RdRand performance was impacted as expected but given that RdRand / RDSEED is not used prolifically especially by desktop workloads, for the other benchmarks the performance was basically unchanged.