Já někde psal o desktopu? Tak určitě na desktopu provozuješ hned několik SQL instancí a aplikace využívající RNG instrukcehnizdo píše:Ano, zcela urcite.
When it came to evaluating different desktop workloads on the Core i5 8400, the RdRand performance was impacted as expected but given that RdRand / RDSEED is not used prolifically especially by desktop workloads, for the other benchmarks the performance was basically unchanged.
Intel CPU design flaw |Meltdown, Spectre a ine|
- Krteq
- Středně pokročilý

-
- Registrován: 22. dub 2005
- Bydliště: Brno
Re: Intel CPU design flaw |Meltdown, Spectre a ine|
- hnizdo
- Začátečník

- Registrován: 29. bře 2007
- Kontaktovat uživatele:
Re: Intel CPU design flaw |Meltdown, Spectre a ine|
Takze jeste jednou.Krteq píše:Já někde psal o desktopu? Tak určitě na desktopu provozuješ hned několik SQL instancí a aplikace využívající RNG instrukce
The "good" news is that RdRand isn't used prolificily by real-world workloads. So when stressing a wide range of server-ish workloads, the overall impact from the SRBDS mitigation was not impacted to within a few percent the original performance as a worst case.
Nekolik procent je tedy dle tebe naprosto nepouzitelne.
MB: Asrock Z690 Extreme CPU: Core i9-12900K cooler: Be quiet! Dark Rock PRO 4 RAM: 32GB 2x16 DDR4-3600 CL16 Kingston Renegade, VGA: MSI 4090 Suprim Liquid SSD: Samsung 960Pro 1TB + EK-M.2 HS HDD: 3TB Toshiba, 18TB WD DC HC550, 8TB Seagate SMR, 2x12TB HGST DC HC520 - RAID1, Optical: LG BH16NS55 BR-RW , Mouse: Logitech G502X Keyb.: Logitech G15+G13+F710, Case: BQ Dark Base PRO 900 r2 PSU: Seasonic Platinum 860W SS-860XP2, Monitor: Asus ROG Swift PG32UCDP, Repro: Logitech Z-5500, Headset: Logitech G935, OS: Win11/64 Pro
>>>>Fórum pro much VRAM much doge věrozvěsty otevřeno! Vstup ZDARMA<<<<
>>>>Fórum pro much VRAM much doge věrozvěsty otevřeno! Vstup ZDARMA<<<<
- mr.qeg
- Začátečník

-
- Registrován: 05. srp 2007
- Bydliště: Dresden
Re: Intel CPU design flaw |Meltdown, Spectre a ine|
Nemohly by tyto instrukce mít uplatnění v kryptografii, což už by real-world bylo? Ale nevím, budu muset pogooglit.
- Krteq
- Středně pokročilý

-
- Registrován: 22. dub 2005
- Bydliště: Brno
Re: Intel CPU design flaw |Meltdown, Spectre a ine|
Tak z nejpoužívanějších SW využívající RDRAND je třeba OpenSSL atd.
A ano, cokoliv "crypto" používá RNG, záleží pak na implementaci v SW jestli přímo používá instrukce RDRAND, RDSEED apod.
A ano, cokoliv "crypto" používá RNG, záleží pak na implementaci v SW jestli přímo používá instrukce RDRAND, RDSEED apod.
- killerek
- Začátečník

-
- Registrován: 09. pro 2003
- Bydliště: Praha
Re: Intel CPU design flaw |Meltdown, Spectre a ine|
Tak to by mohlo byt neprijemne i pro Checkpoint FW, ktere se nasazuji i jako virtualky. Ono i v tech Checkpoint boxech je Xeon.
- Krteq
- Středně pokročilý

-
- Registrován: 22. dub 2005
- Bydliště: Brno
- Krteq
- Středně pokročilý

-
- Registrován: 22. dub 2005
- Bydliště: Brno
Re: Intel CPU design flaw |Meltdown, Spectre a ine|
Další zranitelnost Intel CPUs (+ ARM)
Branch History Injection aka "Spectre-BHB" (CVE-2022-0001, CVE-2022-0002)
Phoronix.com - BHI: The Newest Spectre Vulnerability Affecting Intel & Arm CPUs
Branch History Injection aka "Spectre-BHB" (CVE-2022-0001, CVE-2022-0002)
Phoronix.com - BHI: The Newest Spectre Vulnerability Affecting Intel & Arm CPUs
- Krteq
- Středně pokročilý

-
- Registrován: 22. dub 2005
- Bydliště: Brno
Re: Intel CPU design flaw |Meltdown, Spectre a ine|
... a dopad oprav na výkon u nových CPUs 
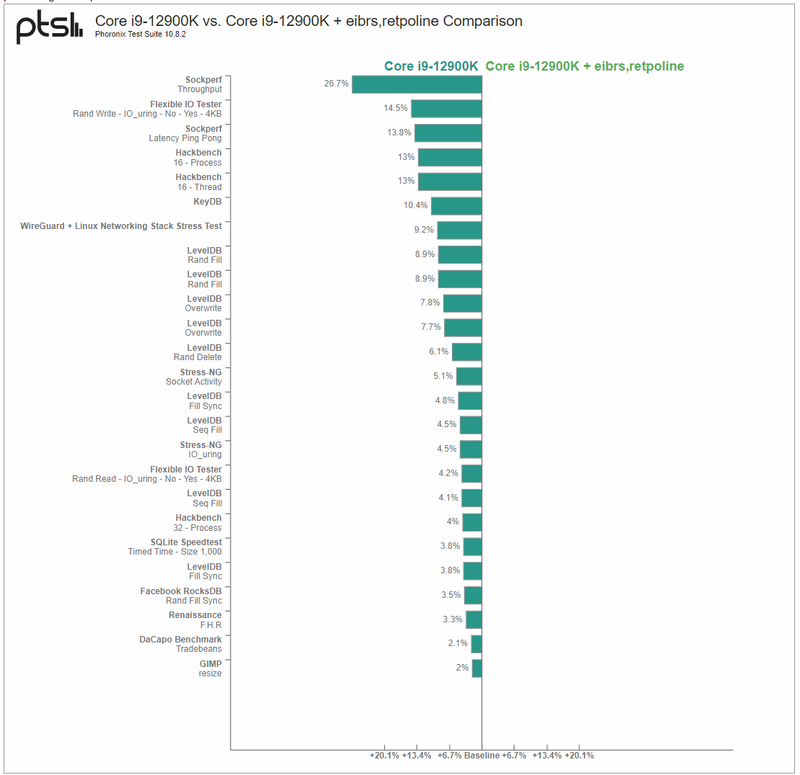

Phoronix.com - In Light Of Spectre BHI, The Performance Impact For Retpolines On Modern Intel CPUs
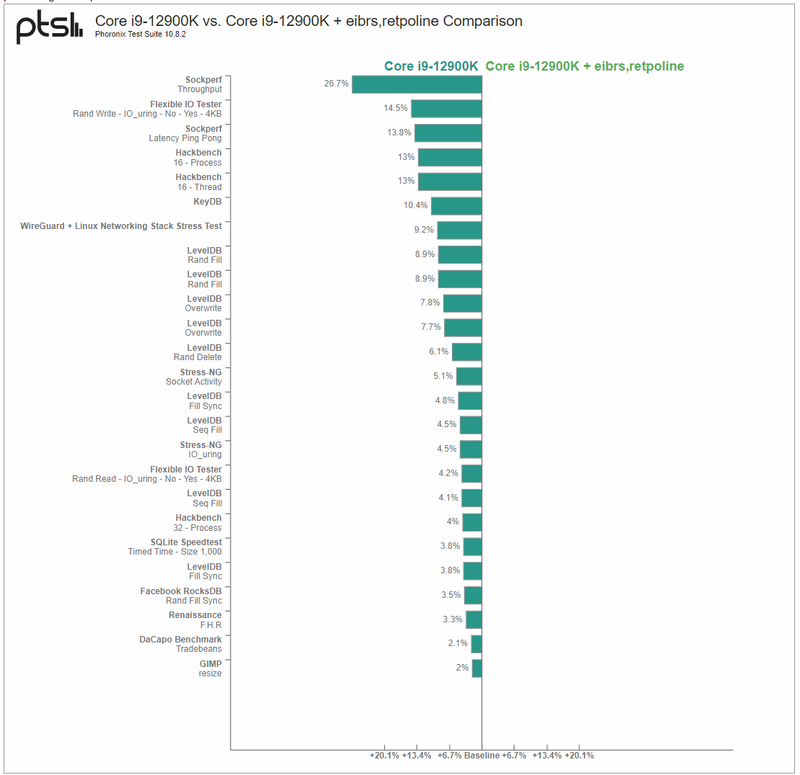

Phoronix.com - In Light Of Spectre BHI, The Performance Impact For Retpolines On Modern Intel CPUs
- hnizdo
- Začátečník

- Registrován: 29. bře 2007
- Kontaktovat uživatele:
Re: Intel CPU design flaw |Meltdown, Spectre a ine|
Oho, strašidelné obrázky.
"Gaming, web browser usage, and other conventional desktop tasks not heavy on I/O or networking didn't see any measurable hit with the "eibrs,retpoline" option."
Tak jdeme zase spát.
"Gaming, web browser usage, and other conventional desktop tasks not heavy on I/O or networking didn't see any measurable hit with the "eibrs,retpoline" option."
Tak jdeme zase spát.
MB: Asrock Z690 Extreme CPU: Core i9-12900K cooler: Be quiet! Dark Rock PRO 4 RAM: 32GB 2x16 DDR4-3600 CL16 Kingston Renegade, VGA: MSI 4090 Suprim Liquid SSD: Samsung 960Pro 1TB + EK-M.2 HS HDD: 3TB Toshiba, 18TB WD DC HC550, 8TB Seagate SMR, 2x12TB HGST DC HC520 - RAID1, Optical: LG BH16NS55 BR-RW , Mouse: Logitech G502X Keyb.: Logitech G15+G13+F710, Case: BQ Dark Base PRO 900 r2 PSU: Seasonic Platinum 860W SS-860XP2, Monitor: Asus ROG Swift PG32UCDP, Repro: Logitech Z-5500, Headset: Logitech G935, OS: Win11/64 Pro
>>>>Fórum pro much VRAM much doge věrozvěsty otevřeno! Vstup ZDARMA<<<<
>>>>Fórum pro much VRAM much doge věrozvěsty otevřeno! Vstup ZDARMA<<<<
- Krteq
- Středně pokročilý

-
- Registrován: 22. dub 2005
- Bydliště: Brno
Re: Intel CPU design flaw |Meltdown, Spectre a ine|
Jo tááák, takže workstation a enterprise segment zase přestal existovat? 
- DOC_ZENITH
- Středně pokročilý

- Registrován: 08. kvě 2010
- Bydliště: Praha
- Krteq
- Středně pokročilý

-
- Registrován: 22. dub 2005
- Bydliště: Brno
- hnizdo
- Začátečník

- Registrován: 29. bře 2007
- Kontaktovat uživatele:
Re: Intel CPU design flaw |Meltdown, Spectre a ine|
To je u rtbleed zda se normalni. Stary intely,z Zeny 1 a 2 maji pod linuxem s mitigacemi dvojnasobnou latenci context swicth. I/O, java sly do kopru... Takze to bude vypadat stejne i pod ESXi.
3950x - But more pressing is if using the newer retbleed=ibpb option for issuing Indirect Branch Prediction Barriers as the safest over the untrained return thunks mitigation but with the highest performance impact. Running with Retbleed IBPB mitigations yielded just 75% the completely unmitigated performance or a 20% hit over the default (untrained return thunks)
https://www.phoronix.com/review/amd-3950x-retbleed/5
3950x - But more pressing is if using the newer retbleed=ibpb option for issuing Indirect Branch Prediction Barriers as the safest over the untrained return thunks mitigation but with the highest performance impact. Running with Retbleed IBPB mitigations yielded just 75% the completely unmitigated performance or a 20% hit over the default (untrained return thunks)
https://www.phoronix.com/review/amd-3950x-retbleed/5
MB: Asrock Z690 Extreme CPU: Core i9-12900K cooler: Be quiet! Dark Rock PRO 4 RAM: 32GB 2x16 DDR4-3600 CL16 Kingston Renegade, VGA: MSI 4090 Suprim Liquid SSD: Samsung 960Pro 1TB + EK-M.2 HS HDD: 3TB Toshiba, 18TB WD DC HC550, 8TB Seagate SMR, 2x12TB HGST DC HC520 - RAID1, Optical: LG BH16NS55 BR-RW , Mouse: Logitech G502X Keyb.: Logitech G15+G13+F710, Case: BQ Dark Base PRO 900 r2 PSU: Seasonic Platinum 860W SS-860XP2, Monitor: Asus ROG Swift PG32UCDP, Repro: Logitech Z-5500, Headset: Logitech G935, OS: Win11/64 Pro
>>>>Fórum pro much VRAM much doge věrozvěsty otevřeno! Vstup ZDARMA<<<<
>>>>Fórum pro much VRAM much doge věrozvěsty otevřeno! Vstup ZDARMA<<<<
- Krteq
- Středně pokročilý

-
- Registrován: 22. dub 2005
- Bydliště: Brno
Re: Intel CPU design flaw |Meltdown, Spectre a ine|
Intel Gather Data Sampling/DOWNFALL - údajně vysoký dopad opravy (paper udává "up to 50%") na AVX2/AVX-512 výkon u Core/Xeonů
Intel DOWNFALL: New Vulnerability Affecting AVX2/AVX-512 With Big Performance Implications
Downfall Attacks
Intel DOWNFALL: New Vulnerability Affecting AVX2/AVX-512 With Big Performance Implications
Downfall Attacks
- Krteq
- Středně pokročilý

-
- Registrován: 22. dub 2005
- Bydliště: Brno
Re: Intel CPU design flaw |Meltdown, Spectre a ine|
Další rok, další nášup Intel zranitelností
Training Solo (3 zraintelnosti v jednom "balíku"):
---------------------------------------------
Branch Privilege Injection:
Training Solo (3 zraintelnosti v jednom "balíku"):
- History-based attacks
Affected: All Intel CPUs with eIBRS, including Intel’s latest generation Lion Cove which features the BHI_NO feature. Selected ARM CPUs, see vendor website. - Indirect Target Selection (ITS) (CVE-2024-28956)
Affected: Multiple Intel CPU generations (i.e., Intel Core 9th-11th, Intel Xeon 2nd-3rd). Please refer to Intel’s advisory for a complete list. - Lion Cove BPU issue (CVE-2025-24495)
Affected: Intel CPUs with Lion Cove core (Lunar Lake / Arrow Lake)
---------------------------------------------
Branch Privilege Injection:
COMSEC - Branch Privilege Injection: Exploiting Branch Predictor Race ConditionsIntel has developed a microcode update for affected processors and provided us with one to evaluate on Alder Lake. We were able to verify that the microcode update stops our primitives that we use in the paper to detect the vulnerabilities. Our performance evaluation shows up to 2.7% overhead for the microcode mitigation on Alder Lake. We have also evaluated several potential alternative mitigation strategies in software with overheads between 1.6% (Coffee Lake Refresh) and 8.3% (Rocket lake). Please refer to our paper for more details.
...
- Is my machine affected?
All intel processors since the 9th generation (Coffee Lake Refresh) are affected by Branch Privilege Injection. However, we have observed predictions bypassing the Indirect Branch Prediction Barrier (IBPB) on processors as far back as 7th generation (Kaby Lake).
- Does Branch Privilege Injection affect non-Intel CPUs?
No. Our analysis has not found any issues on the evaluated AMD and ARM systems.

